We’ve come to learn more about speculative execution since the first Meltdown and Spectre flaws came to light, the performance-enhancing feature found in modern CPU architectures allow a CPU to process data before it’s actually requested by a program or…
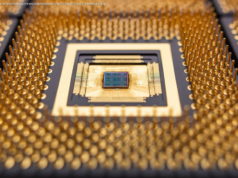
We’ve come to learn more about speculative execution since the first Meltdown and Spectre flaws came to light, the performance-enhancing feature found in modern CPU architectures allow a CPU to process data before it’s actually requested by a program or user. The benefit is that the CPU can concurrently process more data instead of sitting idle if resources are available. By trying to predict an outcome, CPUs can execute certain tasks ahead of time, making the system perform significantly faster.
What nobody anticipated however is that speculative execution would open the doorto manyhard vulnerabilities that cannot be fixed outright but can be mitigated. According to RIDL (Rogue In-Flight Data Load) and Fallout’s informational website (also see, ZombieLoad), these new flaws allow attackers to leak confidential data by exploiting Microarchitectural Data Sampling (MDS) side-channel vulnerabilities in Intel CPUs. Unlike previous Meltdown, Spectre and Foreshadow CPU flaws, the leaks do not occur at the CPU cache level but target arbitrary in-flight data from CPU internal buffers. Qualcomm and AMD processors are not affected by these flaws.
In terms of practical use, security researchers say an attack could be launched using malicious JavaScript in a web page or from a co-located Virtual Machine in the cloud, allowing them to leak confidential data present on your system such as passwords or crypto keys.